
Lab #1: Steganography
Objective
During this activity, students will be able to:
- Design and implement an image processing algorithm using bitwise operations in order to solve a steganographic problem.
Required Software
For this activity you will need to install the Pillow library and its type stub package. At the terminal type:
pip install pillow types-Pillow
Check the Pillow documentation for information on how to use this library.
Description
- ste·ga·no·graph·y (noun)
- The practice of concealing messages or information within other nonsecret text or data.
This activity must be developed in the pre-assigned teams of two.
We have the following processed PNG image file (click on the image to download it):

scarlett.pngOriginal image source: https://wallpaperaccess.com/full/5910215.jpg
There are three independent 1-bit images hidden in the least significant bit of every byte from each of the three color channels of the image.
Write a Python script called extract_hidden_images.py that:
- Takes as a command line argument the name of an RGB mode PNG file. The program should print an error message and quit under the following circumstances:
- Extracts from the red, green, and blue channels the corresponding hidden 1-bit images placing the result in three 1-bit PNG images with the following suffixes after the original extensionless file-name :
- file-name
_channel_1_red.png - file-name
_channel_2_green.png - file-name
_channel_3_blue.png
- file-name
Example
Assuming the above image (scarlett.png) is stored in the same directory as your script you should be able to type at the terminal the following command:
python extract_hidden_images.py scarlett.png
The following three files should be created in the same directory where the scarlett.png file is located:
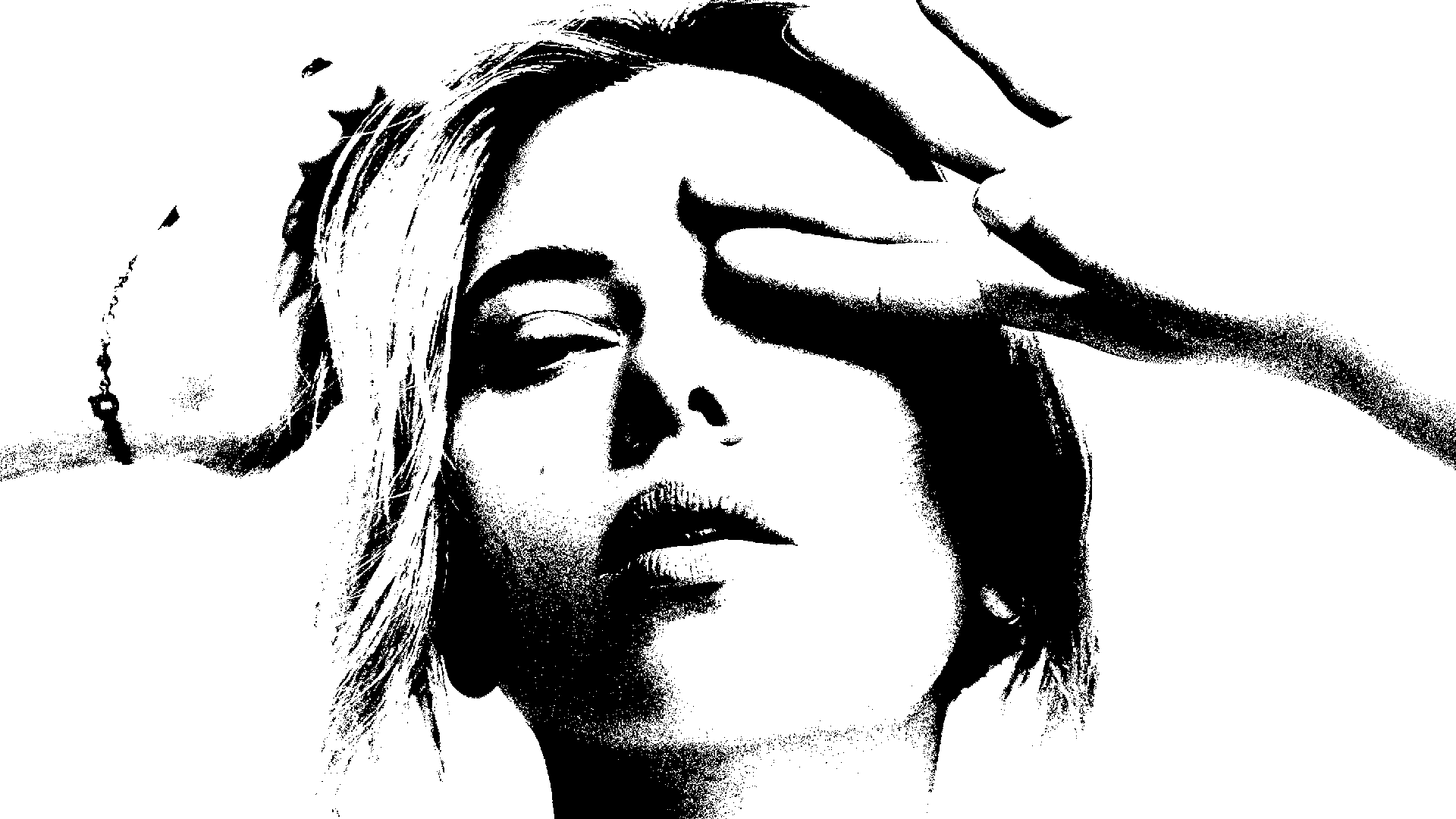
scarlett_channel_1_red.png
scarlett_channel_2_green.png
scarlett_channel_3_blue.pngDeliverables
Place in a comment at the top of the extract_hidden_images.py source file the authors’ personal information (student ID and name), for example:
#---------------------------------------------------------- # Lab #1: Steganography # Image processing through bit manipulation. # # Date: 26-Aug-2022 # Authors: # A01770771 Kamala Khan # A01777771 Carol Danvers #----------------------------------------------------------
Upload Instructions
To deliver the extract_hidden_images.py file, please provide the following information:
Only one team member needs to upload the file.
Due date is Friday, August 26.